Top 9 Pentesting Tools You Need in Your Cybersecurity Arsenal

In today’s cybersecurity landscape, it has now become a question of when rather than why – a service will be attacked. With such a concern in mind, the security takes the center stage. No system is 100% secure and protected. This is why penetration testing (an attempt/or series of attempts to hack/compromise a service) gets the spotlight. It tries to mimic a real-world attack in order to find weak-points/vulnerabilities in a given system that can be exploited.
It is however, different from vulnerability scanning which focuses on identifying the vulnerabilities on predefined components and highlight the potential risks. Penetration testing, on the other hand uses a mix of manual and automated scanning against the target and intends to exploit the found vulnerabilities and/or risks to the max.
There are many tools available, that allows you to primarily scan your target and perform the reconnaissance – which then leads to executing the attack on given vulnerabilities. They are of high-importance, as it saves your time and allow you to focus on potentially weak-areas.
Following are the top 9 penetration testing tools, that you should keep in your pentest tools basket.
1. Nmap
Platform: Windows, GNU/Linux and MacOS
Area: Network scanning and monitoring
The full-form of the name goes as ‘Network mapper’, and is considered as one of the must-have tool for pen-testers. It allows deep analysis of the target network, and lay down all of its characteristics. Those characteristics can include: host, services, OS, packet filters/firewalls etc. It goes way far in revealing the weak-points of a target network and is completely open-sourced.
2. Metasploit
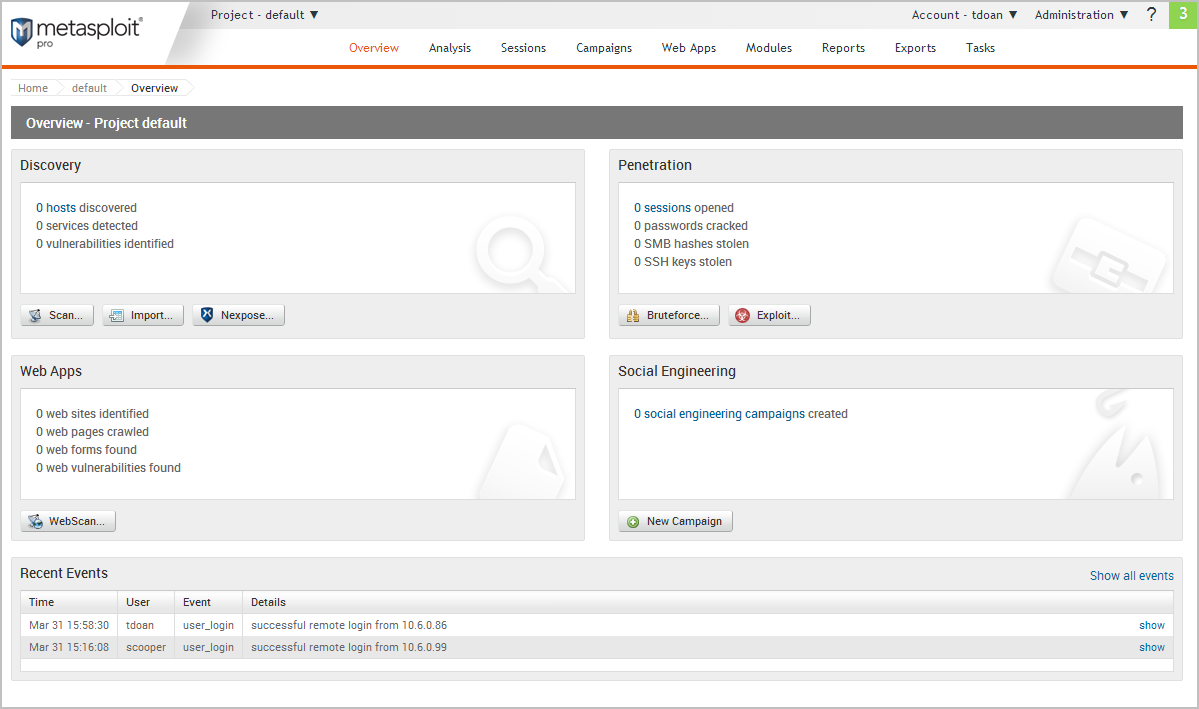
Platform: GNU/Linux
Details: A very popular framework that can be used on web applications, networks and servers. It holds a list of exploits for known vulnerabilities. Upon successful execution, those exploits can run a final payload (to perform desired actions) on the target machine. It offers both command-line and GUI based interface for different platforms. It is a paid product but a free version with limited capabilities.
3. w3af
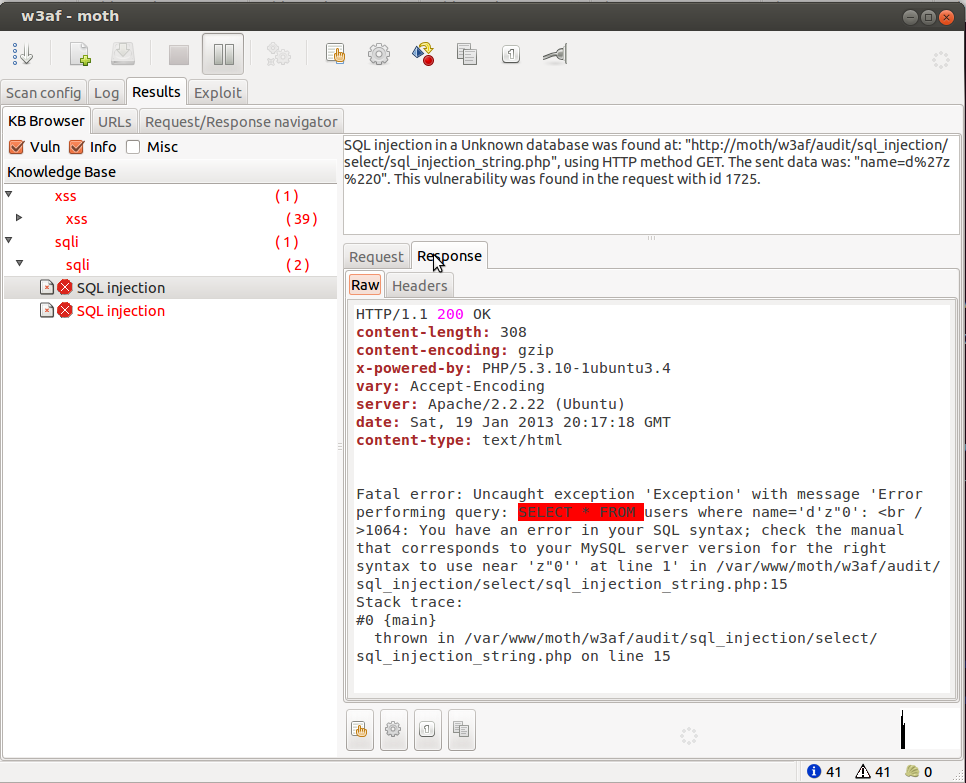
Platform: Windows, GNU/Linux and MacOS
Details: W3afis a Web Application Attack and Audit Framework (as the name suggests) emphasize on web-applications. It integrates web proxy servers and injects payload into different kind of HTTP requests. It is free, based on command-line interface.
4. Zed Attack Proxy (ZAP)

Platform: Windows, GNU/Linux and MacOS
Details: ZAP is a free and opensource scanner and vulnerability finder for web applications. It is made by OWASP, an online ‘web application security’ focused community. It comes with automated scanning, intercepting HTTP requests ability, spiders and much more. Available for all platforms.
5. Burpsuite
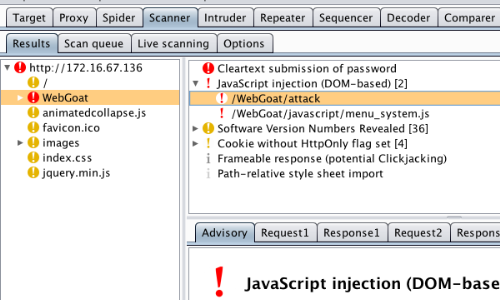
Platform: Windows, GNU/Linux and MacOS
Details: Burp suite provides a powerful proxy and also comes with dedicated (yet limited) attacking capabilities. It often considered as a must-have tool by pentesters. It has both commercial and free version with varying capabilities. Aside from being an intercepting proxy, it also allows crawling content, web application scanning etc. It is available for all platforms.
6. Nessus
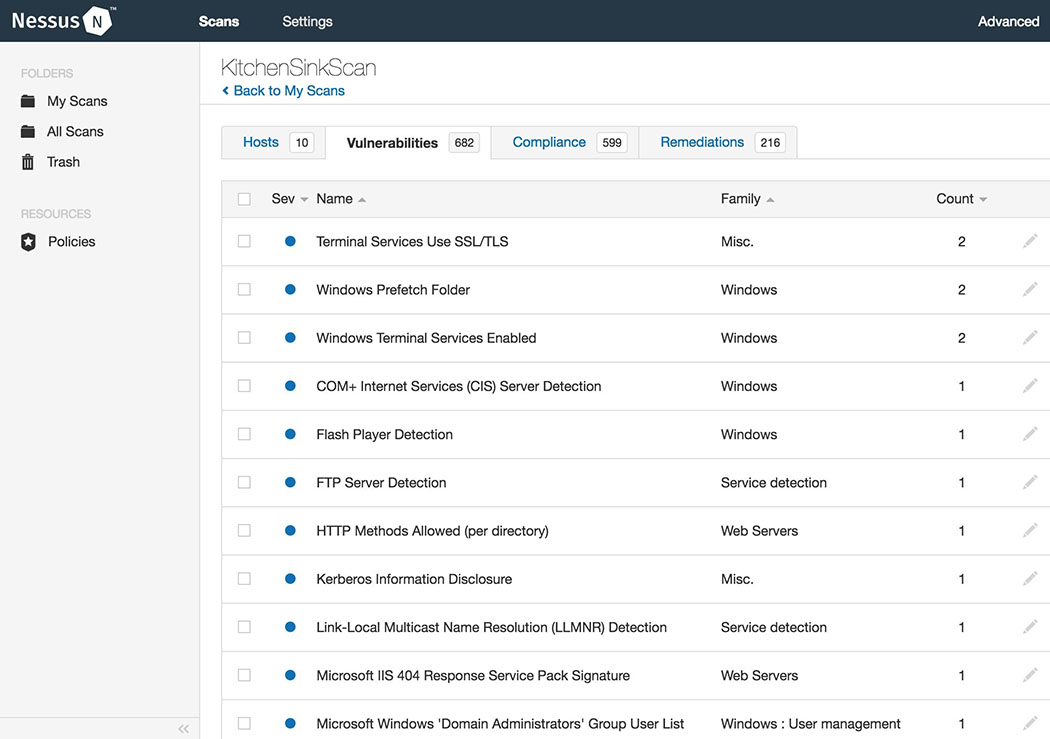
Platform: Windows, GNU/Linux and MacOS
Details: A famous vulnerability scanner, which allow pentesters to go for compliance checks, data leaking points, IP scan, web scanning etc. It has both free and commercial version with varying capabilities – and available for all platforms.
7. SQLmap
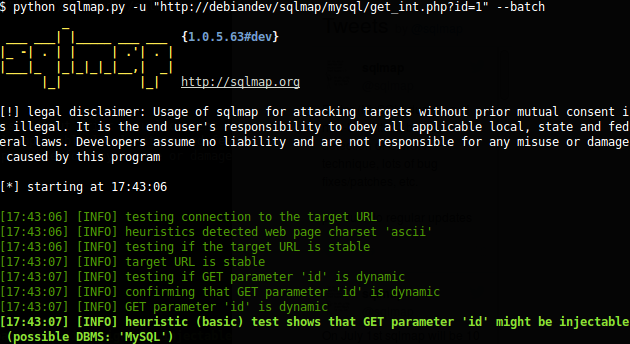
Platform: Windows, GNU/Linux and MacOS
Details: This tool is mainly used for detecting and exploiting SQL injection and other related aspects in an application database servers. It is famous for its craft and is available to all platforms for free.
8. THC Hydra
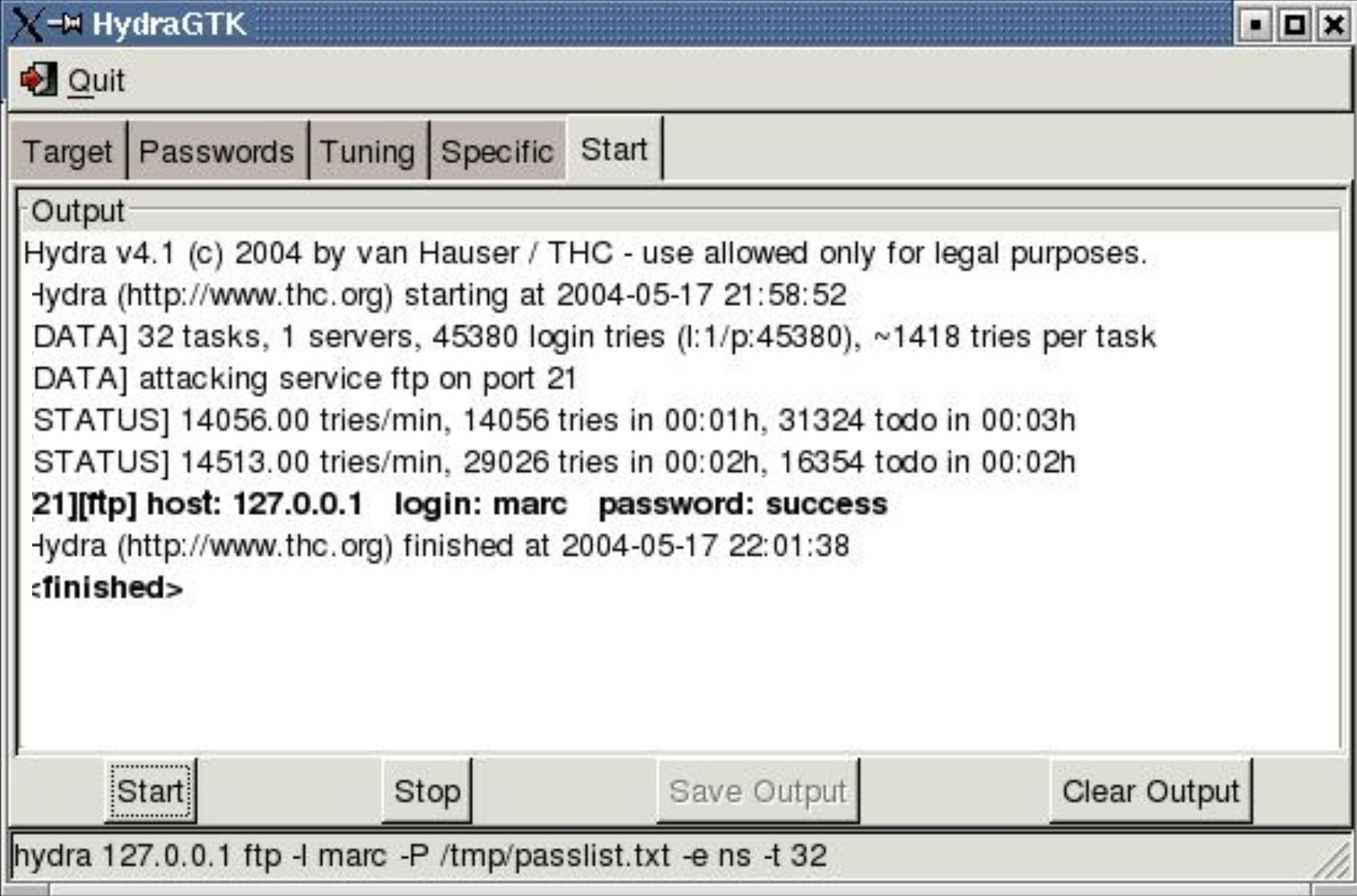
Platform: Windows, GNU/Linux and MacOS
Details: A famous tool in the genre of password cracking ‘THC Hydra’ which is available to all platforms. It is fast and stable that provides dictionary & bruteforce attacks against online login pages (https) and other wide set of protocols including Mail (POP3, IMAP, etc.), Databases, LDAP, SMB, VNC, and SSH.
9. Social Engineer Toolkit
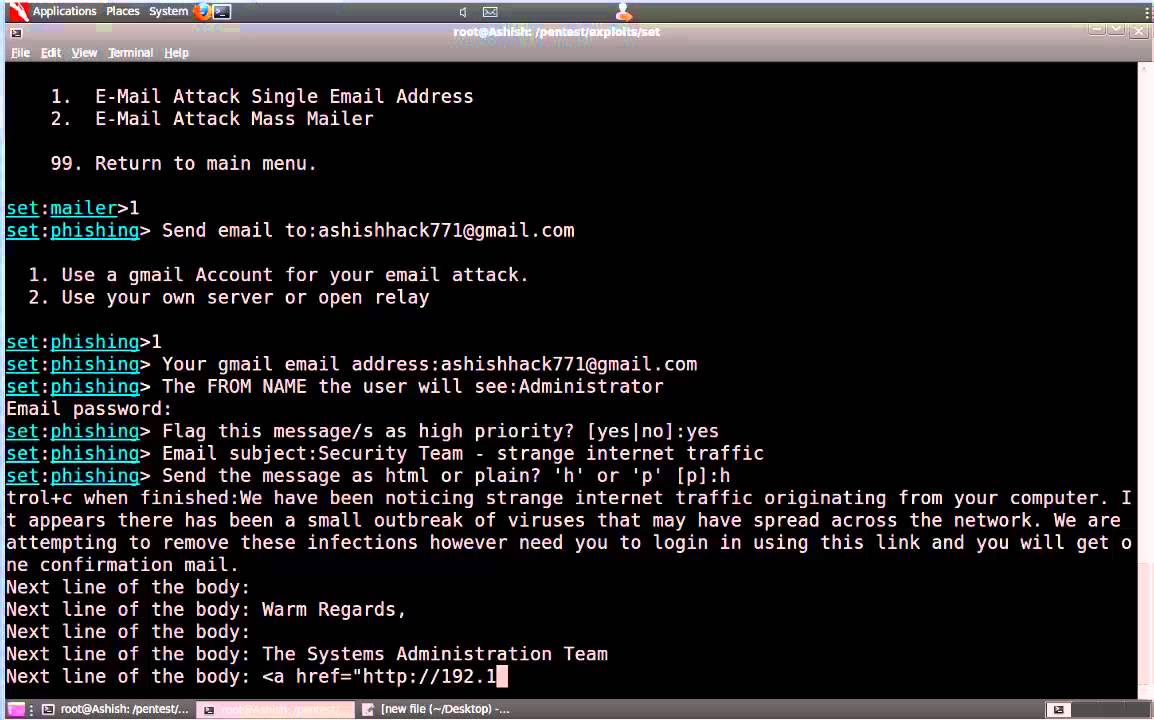
Platform: Windows, GNU/Linux and MacOS
Details: The Social-Engineer Toolkit (SET) is a unique tool-kit that targets the human element than the system element. It allows you to send specially crafted emails with payload (attack code), set phishing pages etc. It is opensource, free to use and comes for all platforms.
Other Tools
- Shodan: a search engine that lets you search for hosts on the internet based on various parameters like city, country hostname, OS, protocols, ports etc. It also allows to search for known vulnerabilities and exploits in the identified hosts.
- Aircrack-ng: a complete suite for pentesting the WiFi that comes with a range of features from capturing data packets to recovering 802.11 WEP and WPA-PSK keys.
- OWASP WebScarab NG Project: A tool to for fuzz testing that involves providing invalid, unexpected, or random data as inputs to an application. The output then monitored for exceptions such as crashes, or for finding potential memory leaks/other weak areas.
- PunkSPIDER: It has its uniqueness in terms of performing multiple scans at once on a given web application.
- Nikto: A scanner that caters to web servers specially to detect outdated software configurations, invalid data and/or CGIs etc.
- Maltego: A tool that focuses on showing/highlighting the relationships between entities and infrastructure of a given environment. The result is a view of inconsistent/not coherent connections and other useful information of the target system.
- OpenVAS: Stands for open vulnerabilities assessment system and as the name says, it scans the target system for known vulnerabilities.
- Sublist3r: A tool that allows pentesters to enumerate the existing sub-domains of a given site. It uses search engines, passive DNS and other brute forcing techniques to achieve its task.
- Wifiphisher: It sets a rogue access point, enabling automated phishing attacks against Wi-Fi networks. Depending on the scope of the job, a pentester can steal credentials or can perform an actual infection.
- Luckystrike: A tool than can generate malicious Excel (.xls) and Word (.doc) documents. Luckystrike can work with standard shell commands, PowerShell scripts, and EXEs.
- As a bonus here’s a little pentest cheatsheet and Seclists.
The above mentioned tools helps a pentester to not only save time, but also draw his attention on right areas. Also, performing a thorough penetration testing not only drops down to picking a list of tools, but instead following a dedicated approach on the focused level (i.e. Network, System, Application), evaluating the organization, assessment information, requirements and stakeholders involved. Nonetheless, the tools have to be complemented with human expertise which should follow ‘white-hat’ approach – as the saying goes “with great power comes great responsibility.”
Sources:
- https://github.com
- http://nmap.org
- http://tenable.com/products/nessus-vulnerability-scanner
- https://www.owasp.org/
- https://www.aircrack-ng.org/
- https://github.com/wifiphisher/wifiphisher
- https://www.paterva.com/
- https://github.com/aboul3la/Sublist3r
- https://www.punkspider.org/
- http://metasploit.com
- http://portswigger.net/burp
- https://github.com/andresriancho/w3af
- https://www.owasp.org/index.php/OWASP_WebScarab_NG_Project
- http://w3af.org
- http://github.com/trustedsec/social-engineer-toolkit/
- https://www.hak5.org/
- http://sqlmap.org
- http://github.com/vanhauser-thc/thc-hydra
- https://twitter.com
- https://www.reddit.com/r/Pentesting/



https://body-rub.manhattan-massage.com/ – nyc bodyrubs
Good day .
Top craftsmen at the present time worth its weight in gold , in this regard prices for Thai massage in Manhattan Beach rather expensive . In our SPA you can find out all the beauty useful procedure practically for nothing .
Relaxing massage of the whole body positive affects all without exception systems and organs our body:
o Muscles and Joints – improved mobility , you will recover faster after a visual load, elimination of lactic acid and recovery from exercise
o Skin – activates flow blood, occurs saturation oxygen
o Vessels – getting rid of edema , normalizing the cardiovascular system and relieving anemia
o Nervous system – improve mood , headaches go away , improve health, relief from headaches and spasms , relieve nervous tension and improve well-being .
Swedish massage more important in case losing weight and getting rid of c ellulite.
The Luxurious Classic massage in Ditmars waiting customer here.
o Impressive variety options massage techniques
o Sessions Hardware – vibration full body massage from 1 hour
Offer all of you , visit the site and learn all methods of massage personally.
buy chloroquine singapore
plaquenil for sale https://hydroxychloroquinex.com/ chloroquine hydroxychloroquine what is hydroxychloroquine
how much is a prednisone prescription side effects for prednisolone
chloroquine buy
hydroxychloroquine eye https://plaquenilx.com/# hydroxychloroquine sulfate uses
tadalafil troche https://www.pharmaceptica.com/
prednisolone side effects effects of long term prednisone use
side effects of accutane roaccutane side effects
goodrx modafinil buy modalert online
Trimethoprim 100mg trimethoprim sulfamethoxazole